- info@syslogicllc.com
- +1.903.224.0088
- 300 East State Highway 243, Canton, Texas 75103

In today’s rapidly evolving threat landscape, businesses need proactive and intelligent security solutions to protect their digital assets. As a proud partner of ESET, we provide industry-leading endpoint protection designed to defend against malware, ransomware, phishing, and advanced persistent threats (APTs).
ESET’s award-winning technology combines signature-based detection, behavioral analysis, and machine learning to detect and block threats in real time.
Engineered for minimal system impact, ESET’s solutions provide robust security without slowing down your network or devices.
With AI-driven threat intelligence, exploit blocking, and fileless malware protection, ESET safeguards your endpoints against even the most sophisticated cyberattacks.
ESET prevents ransomware attacks by detecting suspicious behavior and blocking unauthorized encryption attempts.
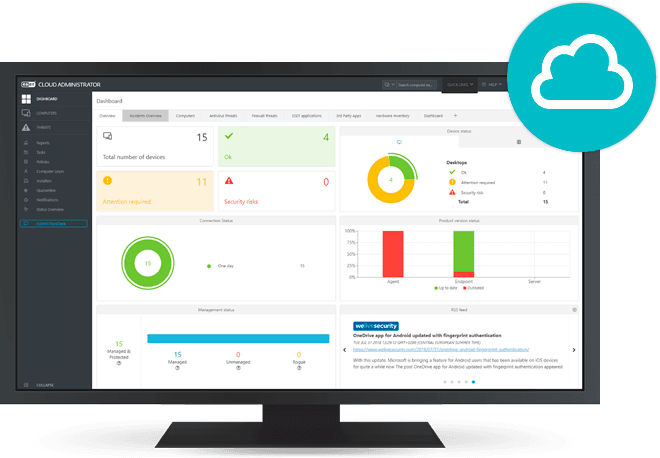
Easily manage security policies, threat monitoring, and compliance across all endpoints with ESET PROTECT, a powerful cloud-based security console.
Built-in endpoint encryption and data loss prevention help businesses meet GDPR, HIPAA, PCI-DSS, and other regulatory requirements.

Advanced protection for Windows, macOS, and Linux endpoints.

Robust security for file servers, ensuring data integrity and business continuity.
Protects sensitive business data by encrypting entire drives.
Flexible security management tailored to your IT environment.

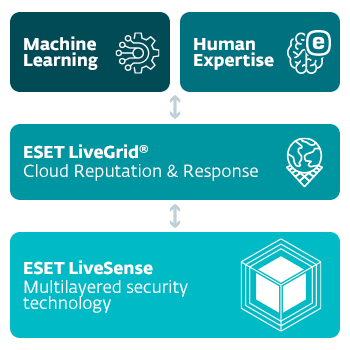
A single layer of defense is not enough in today’s constantly evolving threat landscape. ESET employs a multitude of proprietary, layered technologies, working together as ESET LiveSense, that goes far beyond the capabilities of basic antivirus. We also use advanced machine learning, which ESET pioneered to combat emerging threats. And we were among the earliest adopters of cloud technology, which powers our ESET LiveGrid® global reputation system to constantly update threat intelligence. Advances like these are the work of ESET’s team of dedicated people, who have been researching malware and innovating technology for more than three decades.
ESET LiveSense technology, combined with our machine learning expertise, cloud reputation system, and our people, together power the world’s most formidable cyber threat prevention, detection and response platform.
ESET was the first endpoint security provider to add a dedicated layer into its solution that protects the Unified Extensible Firmware Interface (UEFI). ESET UEFI Scanner checks and enforces the security of the pre-boot environment so that it is compliant with the UEFI specification. It is designed to detect malicious components in the firmware and report them to the user.
Detection types range from very specific hashes to ESET DNA detections, which are complex definitions of malicious behavior and malware characteristics.
While malicious code can be easily modified or obfuscated by attackers, the behavior of objects cannot be changed so easily. ESET DNA detections are designed to take advantage of this principle.

ESET products utilize two different forms of Advanced Machine Learning – a high-powered detection engine in the cloud and a lightweight version on the endpoint. Both employ a handpicked array of classification algorithms; among others, deep learning and boosted trees, that ensure rapid and accurate analysis necessary to stop emerging threats.
The ESET Cloud Malware Protection System is one of several technologies based on ESET’s LiveGrid® cloud system. Unknown, potentially malicious applications and other possible threats are monitored and submitted to the ESET cloud via the ESET LiveGrid® Feedback System.
When inspecting a file or URL, before any scanning takes place, our products check the local cache for known malicious or allowlisted benign objects. This improves scanning performance. Afterwards, our ESET LiveGrid® Reputation System is queried for the object’s reputation (i.e. whether the object has already been seen elsewhere and classified as malicious). This improves scanning efficiency and enables faster sharing of malware intelligence with our customers.
ESET Host-based Intrusion Prevention System (HIPS) uses a predefined set of rules to look for suspicious activities and to monitor and scan behavioral events such as running processes, files and registry keys. When identified, HIPS reports the offending item and – if further analysis is necessary – requests deeper inspection using other ESET technology layers.
Today’s malware is often heavily obfuscated and tries to evade detection as much as possible. To see through this and identify the real behavior hidden underneath the surface, we use in-product sandboxing. With the help of this technology, ESET solutions emulate different components of computer hardware and software to execute a suspicious sample in an isolated virtualized environment.
Advanced Memory Scanner is a unique ESET technology which effectively addresses an important issue of modern malware – heavy use of obfuscation and/or encryption. To tackle these issues, Advanced Memory Scanner monitors the behavior of a suspicious process and scans it once it decloaks in memory.
While ESET’s scanning engine covers exploits that appear in malformed document files and Network Attack Protection targets the communication level, the Exploit Blocker technology blocks the exploitation process itself.
ESET Ransomware Shield is an additional layer protecting users from ransomware. This technology monitors and evaluates all executed applications based on their behavior and reputation. It is designed to detect and block processes that resemble ransomware’s behaviors.
ESET also uses a broad line of detection technologies to identify threats attempting to penetrate victim’s environment on the network level. The list includes detection of malicious network communication, exploitation of yet unpatched vulnerabilities and brute-force attacks against a variety of protocols such as Remote Desktop Protocol, SMB and SQL.
Our Connected Home layer has been designed to reveal what is happening on users’ Wi-Fi networks and get the most out of their connected devices and smart home setups. It also helps users identify vulnerabilities in their home networks such as unpatched firmware flaws in their routers, open ports and weak router passwords.
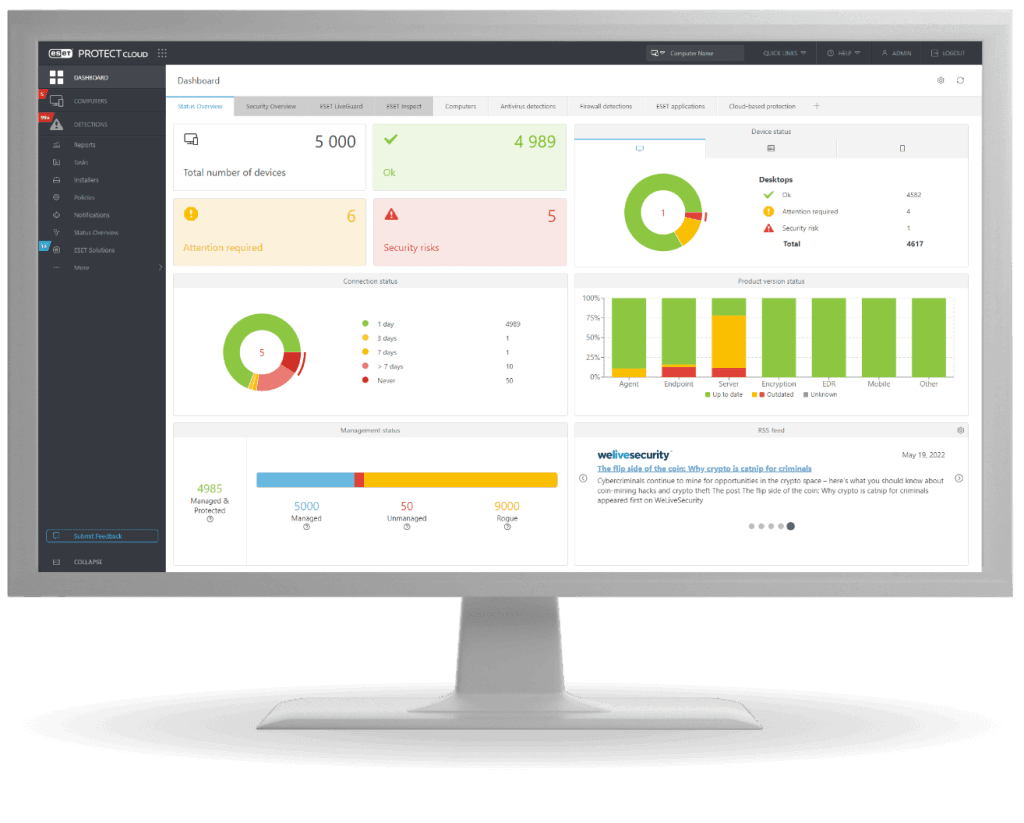
Easily manage security policies, threat monitoring, and compliance across all endpoints with ESET PROTECT, a powerful cloud-based security console.
Contact us today to learn how ESET’s endpoint protection can help you stay ahead of cyber threats and secure your IT environment.